Overview of Smart Plugs Can Be Used By Hackers To Gain Access To Your Home Network
Experts warn that inexpensive smart plugs like the Sonoff S26 and Ener-J WiFi expose users to serious cybersecurity risks. A&O IT Group found these devices use unencrypted HTTP on port 80 and weak factory passwords, enabling attackers to capture Wi-Fi credentials. With network access, criminals can intercept audio/video, control devices, steal data, track traffic, download illegal material, or attack others while remaining untraceable. A&O IT Group notified manufacturers but received no response. CNX Software recommends placing IoT devices on a guest SSID to isolate them from important devices.
Quick Solutions to Questions related to Cheap Smart Plug Vulnerabilities:
-
How can cheap smart plugs expose my home network?
The Sonoff S26 and Ener-J WiFi send unencrypted HTTP traffic on port 80 and use weak factory passwords, enabling attackers to steal Wi-Fi credentials and access the network. -
What can attackers do if they gain my Wi-Fi keys via a vulnerable smart plug?
Attackers can receive video and audio from smartphones, control compromised smart devices, download confidential data, track traffic, and launch attacks on other devices. -
Can hackers remain untraceable when using a compromised smart plug?
The article states attackers could download illegal material or attack other users with virtually no chance of being caught. -
Have the manufacturers been notified about these vulnerabilities?
A&O IT Group says it notified Sonoff and Ener-J but has yet to hear back from either manufacturer. -
What is the recommended immediate mitigation to reduce risk?
CNX Software experts recommend setting up a guest SSID for IoT devices so important devices do not share the same network.
Experts believe cheap smart plugs are a big cybersecurity flaw that could be quickly used by hackers to gain access to a person’s devices or even house.
A&O IT Group outlined its security review of two inexpensive and readily accessible smart plugs, the Sonoff S26 and the Ener-J WiFi, in a blog post.
These smart plugs, which can be purchased for as little as $10 on Amazon, eBay, and Aliexpress, can be used to steal login credentials for the target’s Wi-Fi network. Due to the fact that these devices communicate with the router via port 80, sending unencrypted HTTP traffic, as well as weak factory passwords, this was possible.
If the attackers have the target network’s Wi-Fi keys, they can link to it and do whatever they want, like receiving video and audio from smartphones, manipulating compromised smart devices, downloading confidential data, and even tracking traffic from other devices.
They could also use the Wi-Fi to download illegal material from the internet, or launch attacks on other users’ devices, with virtually no chance of being caught.
A&O IT Group says it has notified both Sonoff and Ener-J of the discovered vulnerabilities but is yet to hear back from either manufacturer.
How To Prevent?
To mitigate the issue, experts from CNX Software, are saying, the quickest way is to set up a guest SSID for the IoT gadgets, so that other important devices don’t share the same network.
Use secured smart Plugs
| Brand | Kasa |
WeMo Mini |
EnBrighten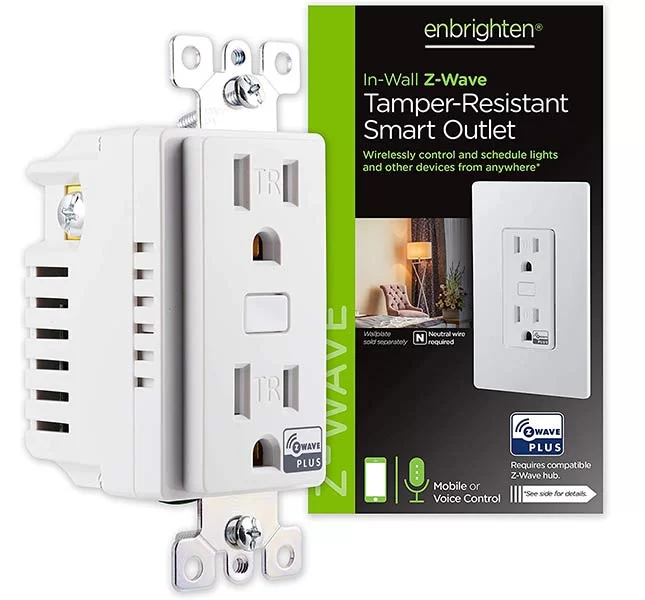 |
| Price | $9.99 | $26.00 | $35.27 |
| Standout feature | Affordable | Away Mode | Z-Wave compatible |




